Overview
In this module we will cover the basics of data security & privacy:
Basic Terminology
Before we continue, let's cover some basic terminology around data security:
Data security refers to protective confidentiality measures that are applied to prevent unauthorized access to computers, databases and websites. Data security also protects data from corruption, also known as data integrity. Data security can also be used to refer to availability of that data when retrieved.

Data privacy is the relationship between the collection and dissemination of data.
Four Personas of Attackers
- The Internal Thief
- The Hactivists
- Organized Crime
- Advanced Persistent Threats (APT) / Nation States
"But I'm just a non-profit, I don't have really important data!!!"
The information that you have *is* of value to anyone who might want it.
Top Organizational Risks for Non-Profits
Financial Costs of Data Breach
In many cases, the financial costs are indirect, meaning commonly not due directly to loss of interest from customers or donors.
- Forensic consultants or investigators
- Lawyers
- Call Centers
- Credit Monitoring for Customers
- Public relations
Generally this comes in the form of reputational risks, and less commonly as fines from government or lawsuits.
Reputational Damage
Reputation costs could include:
- Front Page News, but not in a good way
- Notifying donors, employees, government agencies
- Erosion of Donor Trust
Organizational Lawsuits
- Failing to maintain reasonable data security
- Collecting Personal Data with Payment
- Sharing data with third party without consent
Government Fines
Fines for some of the following types of behaviors:
- Electronic Solicitations
- Donation Platform Breaches
- Donor List Management
- Social Media Outreach
Drivers for Preparation
California S.B. 1386
First law in the United States (2002) that made it a requirement for a company or non-profit which experienced a breach to report it to the customer / consumer.
- Any agency that owns or licenses computerized data that includes personal information
- shall disclose any breach of the security of the system following discovery or notification of the breach in the security of the data
- to any resident of California whose unencrypted personal information was, or is reasonably believed to have been, acquired by an unauthorized person.
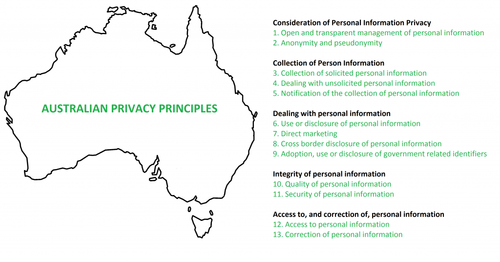
The Privacy Amendment (Notifiable Data Breaches) Bill 2016
The Australian Privacy Amendment specifies breach notification for :
- Australian Government agencies
- Businesses and not-for-profit organisations with an annual turnover of more than $3 million.
It qualifies as an "eligible data breach" when there is a likelihood that the individuals who are affected by the incident are at "risk of serious harm" because their information have been exposed.
Organizations must report to the Privacy Commissioner and affected customers, businesses must include a description of the data breach, what kind of information has been compromised and steps that individuals can take to respond to the incident (such as telling customers to change their passwords on affected online accounts).
Trends We're Seeing Across Industries
Data Collection : Turn Up the Volume
The cost of storing data and processing data is getting cheaper, as a result, we're maintaining more and more data.
- Online Giving : fastest growing fundraising channel
- Social Media : Donor and Constituent Engagement
- Mobile Data : Adding in geolocation considerations and more

Growing Use of Data
Opening the opportunity for analytics and predictive modeling :
- Boost donor network and fundraising
- Extend reach of Services and Solicitations
- Developing new products and services

Data Transfer & Storage
You can't manage all the data yourself - how many of you use any kind of cloud services to house your / your donors data?
- Hosted IT services and cloud-based solutions
- More vendors means more third parties have the data
- Data sharing fosters collaboration

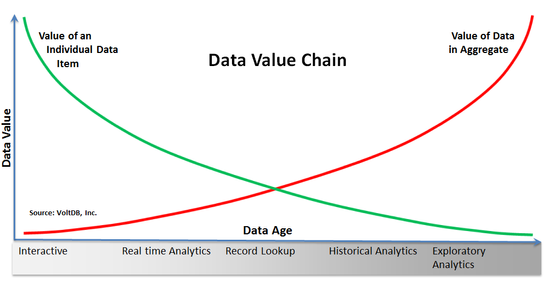
Growing Value of Data
- Data revolution driving all decision-making
- Growing dependence on data and data collection boosts value to those other entities
Let's Talk Data Types
Let's talk about a few types of data, and what considerations should be applied.
Credit Card Data
This is a pretty standard data type. Many of you will accept donations or other giving via credit cards. There are a few standards on how to handle this type of data.
Payment Card Industries Data Security Standard (PCI DSS)
Originally developed by VISA to curb fraud with vendors and credit card processors. The broader credit card industry got together in 2006 to have a single standard across all cards.

Personally Identifiable Information (PII) / Personal Data
Personally identifiable information, or PII, or sometimes referred to as sensitive personal information (SPI), is information that can be used on it's own, or often with additional information, to identify, contact, or location a single person.
Australia's Privacy Act 1988, "personal information" also includes information from which the person's identity is "reasonably ascertainable", potentially covering some information not covered by PII.)
NIST Special Publication 800-122 defines PII as "any information about an individual maintained by an agency, including (1) any information that can be used to distinguish or trace an individual's identity, such as name, social security number, date and place of birth, mother's maiden name, or biometric records; and (2) any other information that is linked or linkable to an individual, such as medical, educational, financial, and employment information."
However, PII is a legal concept, not necessarily a technical concept.
Emergence of Personal Data
- Personal data means any information relating to an identified or identifiable natural person ("data subject"); an identifiable person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, online identifier or to one or more factors specific to the physical, physiological, genetic, mental, economic, cultural or social identity of that person. See Article 4(1) of GDPR.
- Direct identifiers are data elements or fields that identifies a person without additional information or by linking to info in the public domain. For example, name or TFN.
- Indirect identifiers helps connect pieces of information until an individual can be singled out (e.g. DOB, gender. )
| Data Element | Identifier Type |
|---|---|
| Full Name (if not common) | Direct |
| User Name | Direct |
| National ID Number | Direct |
| Passport Number | Direct |
| Email Address | Direct |
| Physical Address | Direct |
| Job Title | Indirect |
| Date of Birth | Indirect |
| Gender | Indirect |
| Time Zone | Indirect |
| Language | Indirect |
| Geolocation Data | Indirect |
What can you do to prepare and protect yourselves?
- Accept that this is an organization-wide issue - NOT just IT and / or IT Security.
This could include the Board, HR, Legal and Audit.
2. Establish technical expertise on the Board, or reporting to the Board.
Security and Privacy are primarily governance issues that need to be addressed from top-down.
3. Identify your organizations most critical data assets.
Where do these assets reside? Who has access to the assets? Do we need to handle them in a particular way?
4. Identify vendors who are being used for business functions involving critical data.
Understand the level of vendor security. Request vendor data security or data privacy certifications to understand how they are working. Incorporate security and privacy language in vendor contracts.
5. Defense-in-depth - assume attackers will penetrate your network.
Firewalls for perimeter, Intrusion detection systems, two-factor authentication, encryption.
6. Encrypt portable devices.
Payroll, PHI or PII. Customer PII. Corporate confidential information.
7. Understand your legal obligations.
PCI-DSS; National / State breach laws; Trade Commissions; European Union (EU).
8. Establish a breach incident response plan.
Establish key teams (likely Legal); establish reporting structure, setup key relationships.
9. Consider an intelligence-led approach to security.
Active traffic / network monitoring. Understand who your attackers are and what they want.
10. Consider buying insurance.
There can be specified security or cyber insurance.